Recently we have noticed increased amount of attacks against online shops using the popular shopping cart software, like WooCommerce, OpenCart etc. In this article we will cover several basics to level up your cPanel server security.
Password strength
Sorry but we have to mention it. The most obvious but the most neglected security advice. Make your passwords really strong. Six characters is not strong. Password containing dictionary words is even less strong. Some time ago we have published an article showing how much time does it take to brute force passwords of different length. Read it to get a basic understanding about what is strong password and what the best practices are.
Everybody wants to use same password for everything, but nowadays it’s no longer an option. Same applies to user names, whenever possible do not use default users, like “admin”, “administrator”, “user”, “test” etc. Good practice is to have your username also randomly generated.
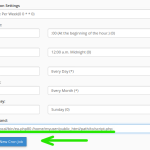
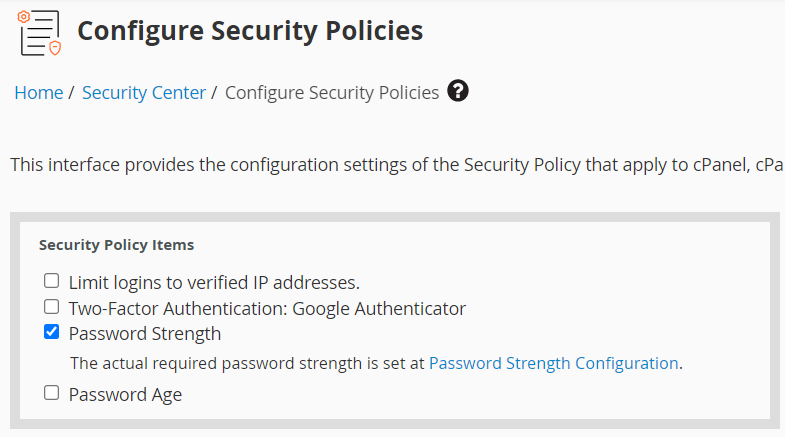
In “WHM > Security Center > Configure Security Policies” there is an option to enforce password strength and age requirement.
Two-Factor authentication
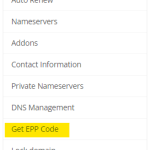
Two-factor is a powerful add up to the security of your server. You can configure 2FA with your Google auth for WHM and cPanel logins.
Go to “Security Center > Two-Factor Authentication” to enable it. First, you will need to “Set-up two factor authentication” within “Manage my account” tab and then toggle “ON” button to enforce the new security policy.
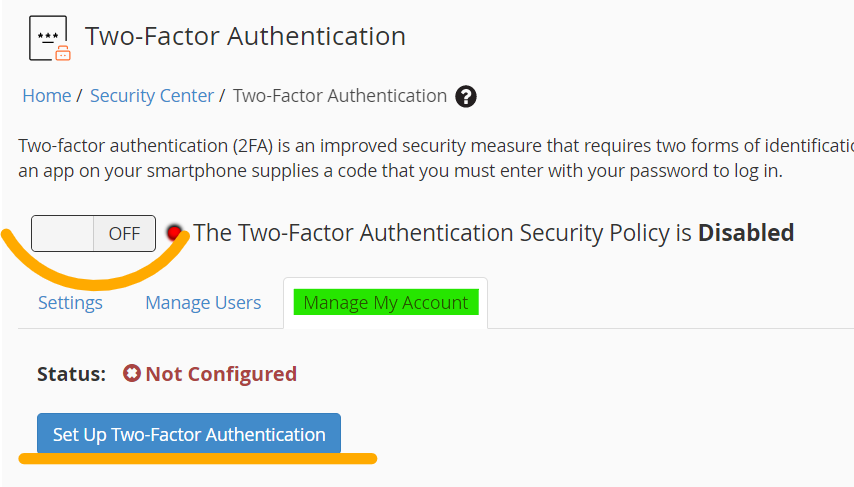
According to the cPanel docs, server time should be accurate in order for 2FA to work correctly.
There is another alike 2FA security option for cPanel/WHM – Security Questions. You can set 4 security questions which will be asked every time you login from unrecognized IP address. If answered correctly, IP will be added to the white-list and you will not be able to answer questions again. Simple but powerful option.

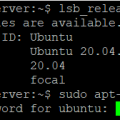
Disable services
Services which you do not use frequently but can be targeted by the hackers- .
- SSH. Go to “Service Configuration > Service Manager“, find SSH Daemon and untick both Enabled and Monitor marks.

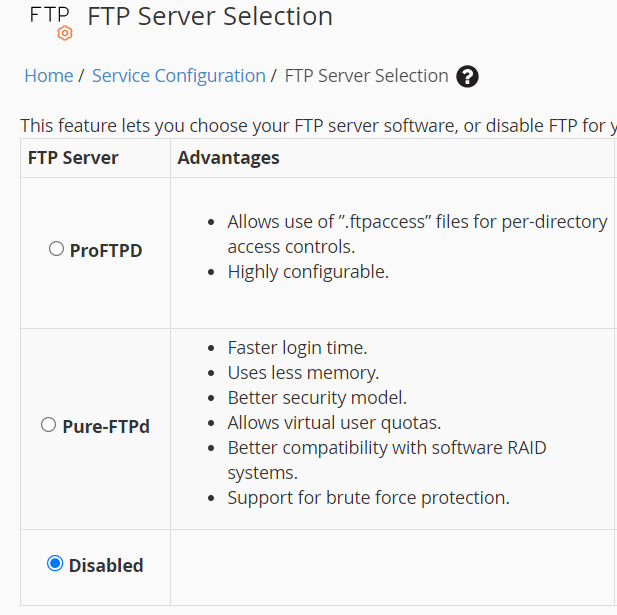
- Turn off FTP. FTP is another common target for the brute-force attacks, nowadays we rarely upload/download files via FTP and generally this service should be disabled. Go to “Service Configuration > FTP Server Selection” and set FTP server to “Disabled”.
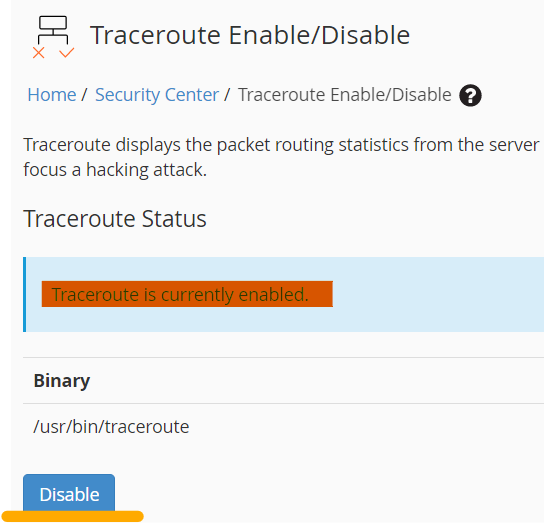
- Traceroute. Hackers can use ping to discover available hosts/servers. Disabling traceroute will make your server non-responsive to ping requests. Go to Security Center > Traceroute Enable/Disable to turn it off.
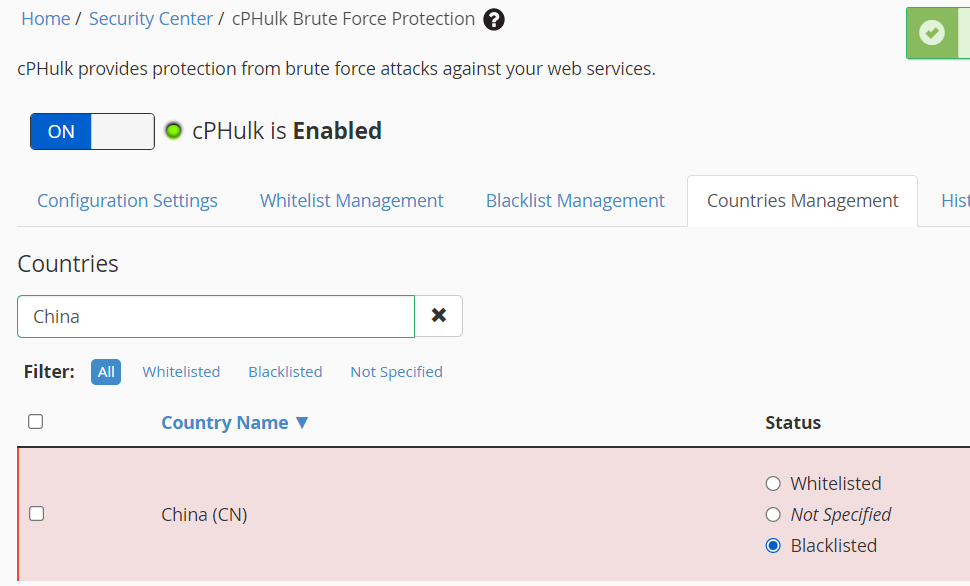
cPHulk
Although cPHulk provides good protection against brute force attacks, sometimes it can be triggered by legit requests as well. We recommend to white-list your known IPs. And if you do not want to reveal your IPs on the system for privacy reasons or you have a dynamic IP, the best way would be to whitelist your VPNs IP address.
The next important feature is Countries blacklist. Most of the attacks are coming from known networks and countries, like China, Brazil and India. Blacklisting those will highly increase your server security. The blacklist applies only to logins to the cPanel server’s services and not to the website access.
Apache Jail
We will not go into much details here since already described it in our previous article. You can read and follow. To keep it short, this tweak hardens the Apache security by segmenting Apache Virtual Hosts in cPanel.
Custom admin URLs
We mean admin login URLs of your shopping cart software. Most of them you can customize, like in WordPress, Prestashop, OpenCart etc. Hackers usually scan known admin paths of popular CMS and they will not be able to test it of the path is modified. We will cover the admin URL change of the popular shopping carts in our next article.