Cloudflare is a popular DNS and traffic proxy provider. Besides it’s known for its robust DDOS protection which in most cases is free, especially when you know how to configure it right. In this article, we will share some of the techniques we at yohost.org use when our customers face DDOS attacks.
Basic configuration
1. Enable proxying
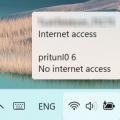
First, you need to make sure that proxying is enabled in your Cloudflare DNS settings and all traffic is directed through Cloudflare. On the Picture 1, you can see where and how to enable traffic proxy. It’s important that proxy is enabled because otherwise attackers can find out your server’s IP and attack it directly.
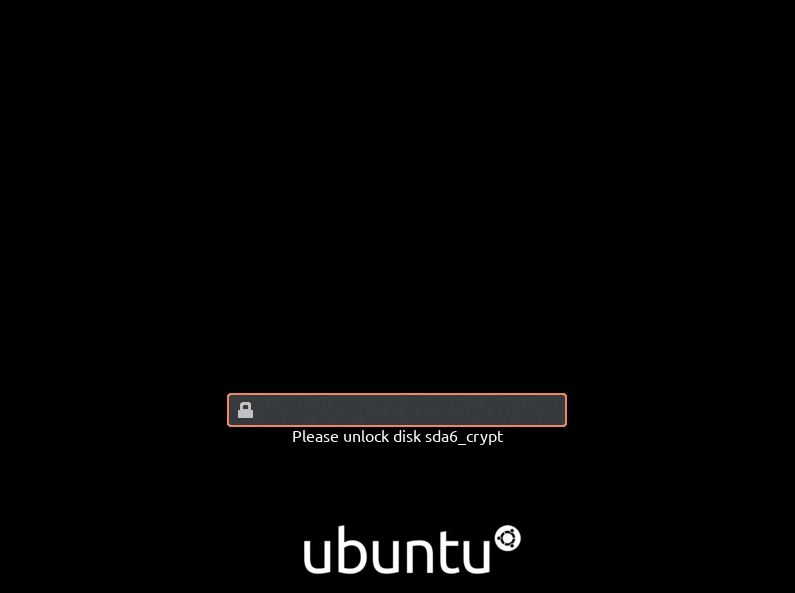
2. One click protection
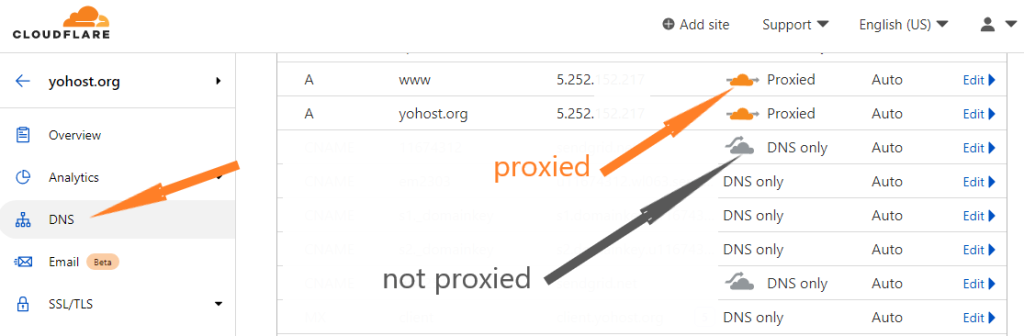
Simple DDOS protection is available with a click of a button. If you enable “Under Attack Mode”, visitors will have to enter CAPTCHA before they can enter the website. On the Picture 2, you can see how to enable “Under Attack” mode.
There are two simple steps you need to take in order to start the fight against attackers. However usually this is not enough if attackers seriously want to take down your website.
Basic-Advanced Configuration
I could not call it Advanced configuration because it’s still Basic for the tech savvy people. But for non-professionals we can call it advanced. The next step is to do a little bit of traffic analysis and configure some Firewall rules.
1. Traffic analysis
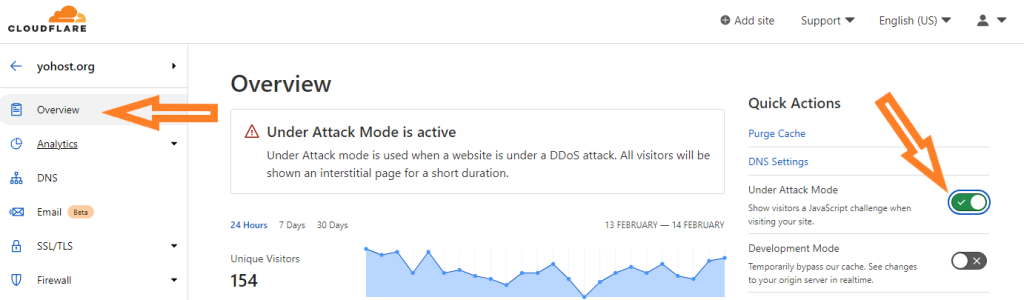
Cloudflare provides a lot of data about your website visitors including showing “good” and “bad” traffic and where it comes from. This data may help you to identify the attackers and apply some Firewall rules to better filter the incoming traffic. Go to “Analytics” > “Security” to find out some information about your incoming traffic. See, Picture 3.
On the picture above you can see that Cloudflare identified 4 threats (visitors) within the last 24 hours and all of them came from Belgium. In this particular case, we are not going to do anything since the threat number is not significant. During attack you can see amount of threats count measured in thousands. In this case you can go ahead and create custom Firewall rules.
2. Firewall configuration
There are quite a few tools available to counter the attack in the free version of Cloudflare. Let’s go through them.
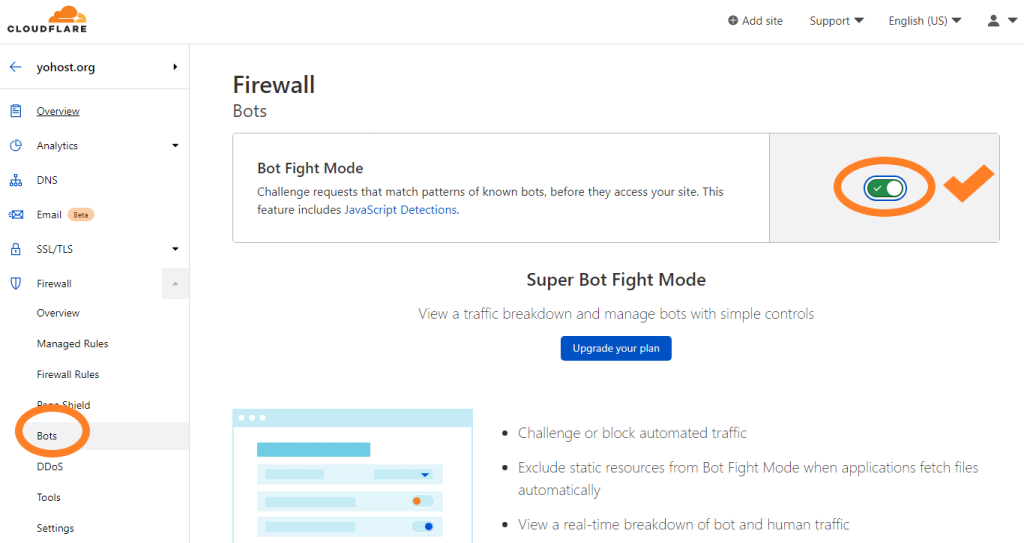
- Bot Fight Mode. This tool aims to protect against attacks with automated traffic. Should be enabled in case of DDOS.
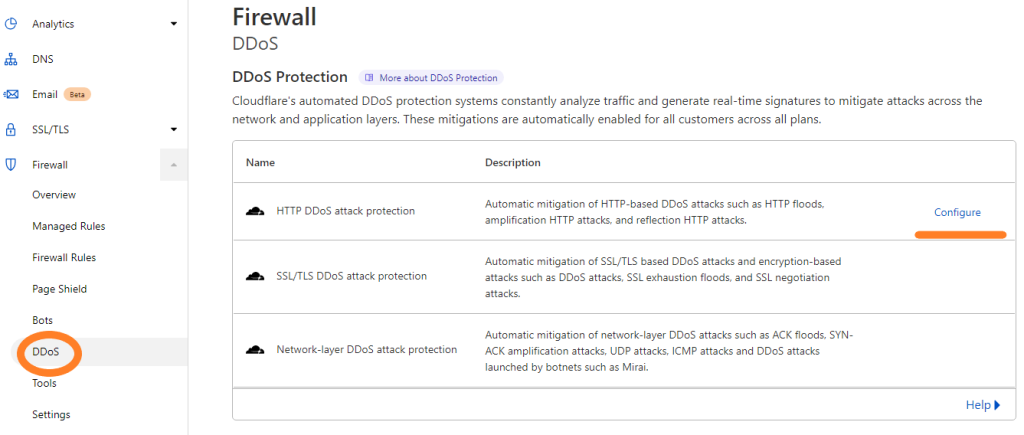
- DDOS protection. This tool provides automated mitigation of DDOS attacks. It analyses your traffic and decides which traffic is good or bad. You can configure Ruleset Action (either to block or show CAPTCHA) and Ruleset sensitivity (The higher the sensitivity is, the more chances that Firewall will block legit traffic). During the attack I recommend to set Rule Sensitivity to High and Rule Action to Captcha.
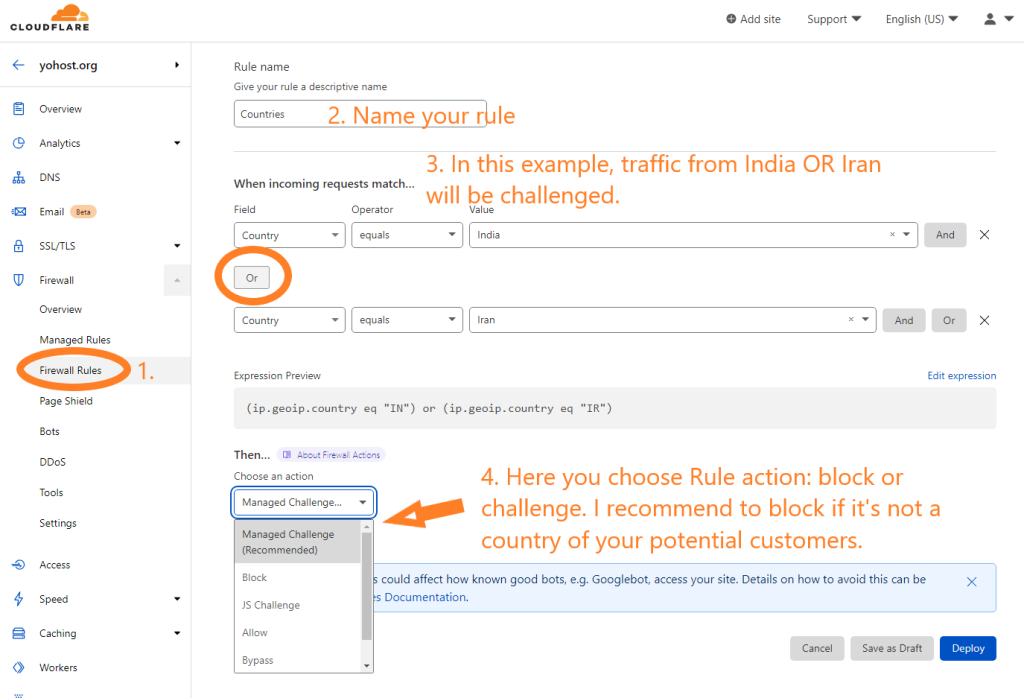
- Firewall Rules. Here you can create custom rules based on the incoming traffic analysis. You can block/challenge certain IPs, Countries, Continents, URL paths, ASNs etc. Mainly you will use these rules to block or challenge countries. Usually, attacks are not coming from the same countries as your customers and sales, so its the easiest and most efficient way to counter the attackers. See the image below for the example of a ruleset.
- About Pro. In most cases Basic configuration you have learned above will be sufficient to stop the attack. However in some cases you will have to go for a Pro version of Cloudflare to enable few more features like WAF (Web application firewall) and Rate Limiting. The latter is one of the most efficient tools against DDOS. It works by limiting amount of requests from one IP. Usually, attackers spam with requests from few IPs, sending hundreds of requests per second while regular users send very few. Rate limiting helps in this case.
Conclusion
From our experience, every attack is different and requires some skills to identify the method of attack and the best way to filter it. When attack starts, its always about how much time your website will be online VS offline during the attack. If attackers see that their attack does not succeed, they will stop it fast because it’s not free to run an attack. So, the main purpose of the technical engineer is to actively counter the attack and adjust protection every time attackers change vector of DDOS. Cloudflare is a good handy tool for this.